a_faerber
Libvirt client for android-arm
an invention by lin_ma
The idea is to port client module of libvirt(x86) to android-arm. Currently, The project only plans to supoort kvm.
virtual wifi adapter in qemu
an idea by lnussel
one of the top features a distribution must always ship in a working state is wireless. Yet we have no way to test it in an automated way. To be able to do that via openQA we need qemu to emulate a wireless adapter. Whether it's emulating existing hardware or implements some virtio device that only works on Linux doesn't matter.
create openSUSE 13.1 images for ARMv7 and ARMv8
an idea by dirkmueller
Currently the last working images for ARMv7/v8 are openSUSE 12.3 based. Since then a lot of new features and regressions have been introduced, so it is time to refresh the appliances based on 13.1 and make them work.
switch to grub2 for powerpc
an invention by k0da
There is a grub2 available for powerpc for a while. Let's switch to it by default.
UEFI on ARM
an idea by gary_lin
Aarch64 was added into UEFI spec recently, and the patches already landed into edk2. The goal of this project is to make an UEFI image to run on the Foundation Model and package Aarch64 edk2 in OBS, so that everyone can just download the latest image and play it.
Package proper cross-compilers
a project by rguenther
openSUSE lacks useable cross-compilers to glibc systems. This is the attempt to provide those, most important a cross-compiler for arm/aarch64.
make openSUSE working on Sony Xperia Tablet Z
a project by sleep_walker
Look once again on Xperia Tablet Z and try to have there openSUSE running natively as alternative operating system.
Bring up Linux on Allwinner A23
a project by rmax
Non-Android Linux can already be booted on several devices that are based on CPUs from Allwinner, such as the A10 and A13, but support for the newer A23 is still incomplete.
Create OpenStack packages for aarch64
a project by dirkmueller
Create a single node installation of OpenStack with the OpenSUSE OpenStack Quickstart scripts for 64 bit ARM (aarch64).
openSUSE on QEMU/AArch64 + UEFI
an invention by gary_lin
The UEFI image for QEMU/AArch64 is available in the openSUSE build service now. However, there is no openSUSE image for that setup. This project is to make openSUSE run on QEMU/AArch64 + UEFI and this may be useful for the openQA in the future.
Say Hello To Ceph!
a project by wanglh
Learn ceph architecture and try to deploy a ceph cluster.
Look into Intel SGX (Software Guard Extensions) for KVM Virtualization
an idea by bfrogers
Learn more about SGX and how that might get used with KVM Virtualization.
Warp speed for virtualization CI testing
a project by jfehlig
The virtualization team's automated testing has a long history. It was born in the old Novell Integration Test framework. The virtualization lab ran an instance of this framework for many years. Over time, those who knew the framework left the company, taking their knowledge and leaving little documentation behind. As our testing needs increased, we found the old framework insufficient, but saw little value in improving it given the available open source CI frameworks.
openSUSE 13.2 ARM hackathon
a project by algraf
openSUSE 13.2 is taking shape on ARM, but we need to make sure we smoothen its edges to make an actual release out of it. The goal of this project is to make sure all devices we should run on actually work and that the last few packages necessary for productive use of ARM devices work properly on 13.2.
Port kGraft to more architectures
a project by vojtech_pavlik
Implement improved ftrace infrastructure for PPC64LE (goal 1), s390x (goal 2), ARM64 (goal 3) that is able to support kGraft and doesn't have a performance impact. PPC64LE has an experimental (untested) patch by Dinar Valeev already, s390x works, but has a 10% performance impact on the system, ARM64 is entirely untouched.
experiments with Pebble smartwatch, including writing a SUSECon application for it
a project by fcrozat
Pebble smartwatch is a nice gadget I own and I'd like to start playing with it at the code level.
Support for automatically building kernels with user-influenced configuration
an invention by vbabka
Sometimes a user might want to build her own kernel instead of using the provided binary, for various reasons. This means creating own .config and maintaining it through kernel version bumps, which often results in running "make oldconfig" and mostly holding down the enter button to accept upstream defaults.
Build openSUSE for m68k
an idea by AndreasSchwab
Lorem ipsum
Faster Raspberry Pi Builds for SUSE Studio
an invention by bkutil
Intro
In order to be able to throw pies faster and distribute them even to remote SUSE colonies, we need to build an advanced antimatter-fueled pie hyper-accelerator.
Resistance is Futile - Using zypper to "upgrade" CentOS/RHEL to openSUSE/SLES
a project by RBrownSUSE
zypper is magic
 openSUSE Landing Page Prototype
openSUSE Landing Page Prototype
a project by hennevogel
www.opensuse.org is the single most accessed page in the SUSE/openSUSE universe. With 1.5 million visits per month it generates 2.5 million page views and has around 500 people on the page at any given time. Yet it's one of the oldest, crufty pages we have!
Get the new SUSE Floor ready to use!
a project by rsalevsky
The new SUSE Floor is nearly done. The core functionality is already implemented and only some basic features are left.
Experiment with no-mmu Linux (STM32F429I-DISCO)
an invention by a_faerber
A broad range of ARMv7-A boards have been enabled in openSUSE already. I would like to complement my experiences by bringing up Linux on an ARMv7-M board, the STM32F429I discovery board, featuring a Cortex-M4 and 8 MB SDRAM.
[ARM] Ceph on AArch64
an idea by algraf
Octopuses have many ARMs, so we should definitely allow them to run on them too!
[ARM] Bootstrap ILP32 on AArch64
a project by algraf
Some customers are still stuck in a world of 32bit. On ARM64, we have two options for those poor folks:
Bare Metal OpenQA
a project by algraf
Today OpenQA mostly runs on virtual machines, but it can get really tricky to find bugs triggered by real hardware. There are only few interfaces required to interact with a machine though:
Automate OMVF/shim/MOK tests
a project by gary_lin
I previously created a semi-auto test script(*) for MOK. The script controls the QEMU virtual machine a pre-setup image and performs two simple test cases. It's tedious to setup the images for every SLE and openSUSE. My goal is to write a script to automatically set up the virtual machines and images and do a full test. I would also like to set up a test for weekly-built OVMF. openQA might be a good reference.
VNC keyboard layout test tool
a project by michalsrb
VNC protocol transfers key symbols (= basically characters), not key codes (= "coordinates" on keyboard). Therefore pressing the same keys may result in sending different commands over VNC depending on the keyboard layout and state of modifiers on the client side. The server however can not directly send the key symbol to the application, it must instead find or create key code that will translate to that symbol and send that.
Get openSUSE running in parallel to Android on a regular and rooted Android Smartphone
a project by sndirsch
Get openSUSE running in parallel to Android on a regular and rooted Android Smartphone. On top of this try to get a graphical desktop running using Xvnc available for Android.
Simple user interface for head mounted displays
a project by chuller
Create a user interface useable with a see through head mounted display. The display was created from some Chinese video glasses and has a low resolution (320x240) which requires a optimized user interface that also is useful when using it hands free.
Provision SLE12 Power compute host with crowbar.
a project by k0da
In order to have complete cloud experience on Power platform it needs some missing pieces to be available: * SLEShammer image (SLE11-> SLE12)
virtio-serial in OpenStack
a project by e_bischoff
Currently, the usual way to communicate with VM instances in the cloud from outside is ssh. This is okay for most uses, but a) does not work when you mess up with the guest's ability to network and b) requires a free floating IP.
Bootstrap Maven in OBS
a project by a_faerber
Apache Maven is a build tool used by many Java projects, which is incompatible with OBS in that it tries to download binary dependencies from the Internet. Several people have in the past years tried to somehow bootstrap Maven and failed.
Create a git project for VMDP
a project by kallan
Needing to learn git, I thought it would be a good time to clean up the code and create a git project for it.
Validation of QEMU storage integrity
an idea by bfrogers
Spurred along by a recently reported bug, I'm producing methods, analysis and hopefully a validation tool to ensure data integrity of our storage formats and caching modes for QEMU storage interfaces.
Continue continuous integration improvements in virtualization
a project by mlatimer
In previous Hackweeks, we've gone to warp speed in our virtualization CI testing through:
Create packages for SLES 12 s390x in obs.
a project by ihno
Create packages for SLES 12 s390x in obs.
Build and boot every commit in the kernel-source tree
a project by michal-m
Or at least, test as many of them as possible.
SUSE office in a box
a project by ancorgs
Working remotely has many advantages, but you sometimes lack some infrastructure. Specially if you use several computers or you share space with other SUSE co-workers. We are 3 Susers in Gran Canaria and we plan to share an office. So we have bought a Cubietruck, a tiny device with minimum power consumption, an ARM processor, a SATA interface and a Gigabit ethernet.
Tool to write raw images to USB disks
a project by alarrosa
The idea would be to create a qt5/kde5 based utility that can use local raw images as well as download a list of sources from a remote site. The idea is to provide a user interface that can be used by any user as well as a user interface that can be used in kiosk mode for booths so that a visitor can put a usb pendrive in any usb slot, select the image he/she wants to write to it and get it written in parallel to other usb memories.
Photobooth with RaspberryPi
a project by digitaltomm
The software is a rails app with an Angular.js frontend using the gphoto2 library to trigger a Nikon D60 camera.
internal "gravatar" with floor icons
an idea by lnussel
set up an internal gravatar clone with floor icons for use in ibs, openqa etc
Ceph RBD backed USB mass storage gadget
a project by dmdiss
Create a USB device that, when configured and connected, exposes one or more Ceph RBD images for use as USB storage, allowing for:
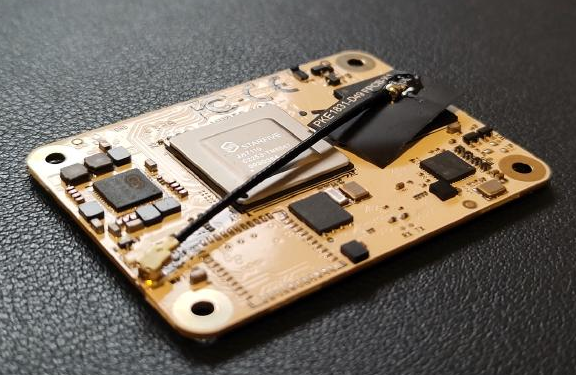
 arm64 set-top-box based workstation
arm64 set-top-box based workstation
a project by mbrugger
Tronsmart has a Rockchip rk3368 based set-top-box [1].
Play with ARM board
a project by nadvornik
Since my Orange Pi board just arrived, I will play with it.
Research on COLO - the HA solution for virtualization
a project by gqjiang
COLO or Coarse Grain Lock Stepping is an High Availability solution that builds on top of Remus,
Multimedia insane migration
a project by scarabeus_iv
Packman reduction
Implement >=z10 (s390x) support to QEMU
a project by mbenes
Last time I checked QEMU lacked support for >= z10 processors. Thus one cannot run SLE12 and newer in a virtual machine on non-s390x host. I'd like to improve the situation during Hackweeks.
Simulate SD card in software
a project by algraf
To make OpenQA work with real ARM devices, we need to control
port coreboot to 96Boards HiKey
a project by vimacs
Hikey is a development board with HiSilicon Kirin 620 eight-core ARM Cortex-A53 64-bit SoC. The original firmware is based on Tianocore EDK II, and I'd like to port coreboot to this board.
FCoE over virtio
a project by hreinecke
This project aims for enabling FCoE over virtio-net. With that we should be able to run FCoE within a KVM guest, and finally have a 'real' FC host in a KVM guest. This should enable 'real' FC testing, like link failure, multipath operations etc.
Get real with NFV on Suse OpenStack Cloud
a project by mmnelemane
The idea behind the project comes from recent work on integration of OpenDayLight with Suse OpenStack Cloud 6/7. The goal for this Hackweek project is to realize a demonstrable NFV use-case on Suse OpenStack Cloud with as much reduced manual orchestration as possible. The use-case to consider is to run a Service Function Chain(SFC) with basic Network functions like Firewall/QoS that run as services on JeOS Guests on SUSE OpenStack Cloud (SOC).
Image for Orange PI PC board
a project by nadvornik
The support for Orange PI PC in mainline kernel has advanced a bit, so now it should be possible to build openSUSE image that has at least serial support with kernel 4.6 and usb support with 4.7. I will investigate this.
Reviving the Nokia N900
a project by mstaudt
The Nokia N900 is a versatile phone/tablet/mini-computer. While its specs are outdated by today's standards, it's still hard to find something equivalently useful to hack on-the-go.
 Faster kernel builds in the OBS
Faster kernel builds in the OBS
an invention by michal-m
The kernel compile and link itself is only a fraction of the OBS kernel-default package build. Several other passes take significant time: - Post build checks, especially the clamav scan
[openSUSE] speed up distro rebuild time by analyzing rebuild graph
a project by lnussel
The openSUSE build service could build hundreds of packages in parallel but in practice serial package dependencies prevent that.
Convert openSUSE ARM appliances to python3-kiwi
an idea by dirkmueller
The python3-kiwi rewrite of kiwi is progressing is far enough to try converting the openSUSE ARM appliances to make use of it. The goal of the project is to build appliances with python3-kiwi and test them to see that they work fine and then switch over if it seems benificial.
Use nfc device to control Raspberry Pi
a project by acho-novell
Goal
Use a Raspberry Pie with the Sense Hat to display messages via Salt
a project by joachimwerner
This was a short 2-hour fun project.
Compile Factory or some components entirely with Address Sanitizer enabled and push it to openQA
an idea by vpereirabr
Following Tizen and other internal initiatives, to have Factory complete or partially compiled with Address Sanitizer and give it openQA a try to "fuzz" it, looking for memory management issues:
Help with mainline support for the Mediatek chromebook (MT8173 based)
a project by mbrugger
Lately the necessary patches to get rudimentary support for the Mediatek chromebook with a mainline kernel got posted. There are some hacks and I'll work on some good solution to get graphics go, at least.
Try more qemu/libvirt features.
a project by xlai
Current virtualization requirements mainly come from fate, and I haven't got chance to try freely many features of qemu/libvirt. So I will try to play it.
Upstream support for SGI Octane
an invention by tsbogend
Patches for supporting SGI Octanes are floating around since ages. The latest version is against v4.10. I've talked to Ralf Baechle (MIPS kernel maintainer) and he is willing to take patches from me... so I have to provide them... and this what this project is for:-)
Upstreaming of mediatek helios board
an idea by mbrugger
The only Mediatek "hacker" board available is from 96 Boards [1]. Unfortunately up to now there is nearly no mainline support. Idea would be to improve this situation. The idea would be to get the pin-controller merged first and then hopefully most of the other stuff can be just added (fingers crossed...)
Upstream support for the NXP LPC313x ARM SoC
an idea by morbidrsa
I have an old NXP LPC313x ARM SoC develboard lying around which has no upstream kernel support, port the ancient 2.6.xx BSP to a recent upstream kernel and submit it.
Create a tool to generate vCPU/vNUMA topology for virtual machines
a project by jfehlig
Most large workloads such as SAP HANA require special, highly optimized configuration to run in a virtual machine. Virtual resources such as memory and CPU must be carefully configured to ensure optimum performance of the virtual machine workload. Default VM configuration created by tools such as virt-install are not optimized and often result in poor performance of large workloads due to memory access latencies and incorrect/incomplete information available to the VM's task scheduler.
 openSUSE on chromebooks (crouton)
openSUSE on chromebooks (crouton)
an idea by mbrugger
Update for 2018
netlink interface for ethtool
a project by mkubecek
There seems to be an overall consensus that the ioctl interface used by ethtool is a poor design as it's inflexible, error prone and notoriously hard to extend. It should clearly be replaced by netlink and obsoleted. Unfortunately not much actual work has been done in that direction until this project started.
 openSUSE/SLE/Mainline U-boot for some not-yet-supported ARM64 boards
openSUSE/SLE/Mainline U-boot for some not-yet-supported ARM64 boards
an idea by ldevulder
The Khadas VIM (http://khadas.com/vim/) is an arm64 DIY Set-Top-Box based on Amlogic P212 reference board that use S905X SoC.
Exploring ZX Spectrum Next's new features
a project by wstephenson
Back in the day, I enjoyed coding on 8 bit machines, mostly MSX. There is now a Kickstarted project to create a successor machine with some new features: hardware sprites, hardware scrolling, better sound, integrated SD/MMC IO and an ESP8266 for networking.
Add SUSE Manager virtualization management capabilities
a project by cbosdonnat
SUSE Manager can do some virtual machines management, but needs a lot to be complete. This project is about investigating more on that topic.
Investigate Oops in SLES 15 on Raspberry Pi
a project by jiriwiesner
I use my Raspberry Pi 3B as a router. I have seen this crash:
work on sunxi a64 cpufreq driver (for teres-1, pine64)
an idea by mbrugger
With the teres-1 [1] laptop we have a first arm64 device we could use as end-users. Much work to run mainline kernel + u-boot was done already. But power consumption of the laptop is not optimal (~2 hours of battery life time).
minimal CRM solution based on Open Source
an idea by hrommel1
To better understand the market / challenges of small CRM solutions, I want to setup a minimal CRM solution that ...
Load balancing and cloud instances with Raspberri Pi
a project by SLindoMansilla
Description
Improved mhvtl package: fix the out-of-stream kernel driver
an idea by lee_duncan
The mhvtl tape library emulation package was originally based on the scsi_debug kernel driver, but has long since grown more complicated, with the mhvtl,ko kernel module now passing almost all SCSI commands to user-level daemons via a clunky device interface. It does this with an out-of-band driver, since the design is so bad it would never be accepted upstream.
UEFI Capsule Update Channel for Minnowboard
a project by gary_lin
Minnowboard is the platform for UEFI development and supports UEFI capsule update since 0.99, and we are supposed to be able to test the feature with fwupd. However, there is no capsule file in fwupd.org or the official firmware download site. Besides, the Minnowboard firmware source in the current edk2/edk2-platforms git couldn't build due to the recent change of directories. My goal is to rebase the Minnowboard build system to the current git master and create a working up-to-date firmware. Signing the firmware properly would be a plus so that we can apply a private repo in fwupd.org for the development or QA testing.
Set up a VM on x86_64 and ppc64le for LTP tests
an idea by osalvador
Set up a VM on x86_64 and ppc64le sitting on linux-next/mmotm running LTP tests in a loop.
Tensorflow on opensuse
an idea by huizhizhao
Background
TensorFlow makes it easy for beginners and experts to create machine learning models for desktop, mobile, web, and cloud. But from installation guide to best practice there're rarely cases mentioned tensorflow on OpenSUSE. So OpenSUSE needs to be introduced to tensorflow community.
Building Image with KIWI
an idea by Jeffreycheung
Well, we know that there are many tools in SUSE to build a image and one of them is KIWI. I would like to find time to study and build the image by KIWI during this hackweek.
Get openSUSE Tumbleweed for s390x (IBM mainframe) on openqa.opensuse.org
an invention by SLindoMansilla
Description
openSUSE image for Samsung DEX
a project by adrianSuSE
I want to get an openSUSE based image working on Samsung DEX:
Dangerous voyage in openSUSE Infrastructure sea.
a project by mcaj
Well the see of openSUSE Infrastructure has been unrest and need our attention. I would like to invite you for this cruise trip.
Demo project for HA using Raspberry pi-s
a project by xarbulu
I have noticed that explaining HA cluster concepts to non technical people is not easy (my parents for example hehe). In order to improve that I would like to create a more visual project using raspberry pi-s.
Test Raspberry Pi
a project by leli
1.Test to burn the opensuse kernel on Raspberry Pi and make it working. 2. Try to use Raspberry Pi to control some sensors.
Explore RISC-V
a project by clin
RISC-V is an open ISA (Instruction Set Architecture) based on RISC architecture. It's originated from UC Berkeley and it's attracting more attention in recent years because of its full open architecture so every developer has opportunities to get involved in application processor design or apply it into different applications, such as IoT, Robotics, ... etc.
PXE improvements for QAM
a project by pluskalm
We kinda need more flexible PXE in Prague office, UEFI would also not hurt - so lets check what we can do to make it better.
Rewrite Jangouts using React/Redux
a project by IGonzalezSosa
We already tried to improve the Jangouts data model in the past and, although we made quite some progress, we did not finish it. I've been playing a bit with React and Redux lately, and I would like now to try a different approach replacing Angular with that combo. Using Vue.js might be another option too.
minimal openQA
an invention by okurz
motivation
Many people ask how to start with openQA, ask "can you run these two lines in bash in an openQA" test and some shun the effort to try out openQA because it is "too big".
Learn about Robotics
an invention by mstrigl
I want to learn more about robotics. The goal is to have a small robot at the end of the week.
PXEAT - A PXE management tool
a project by whdu
PXEAT (stand for PXE Administration Tool) is a tool to easily deploy and manage PXE service.
Easy openSUSE Upgrade
a project by maverick74
The idea is about an easy way to allow users to make upgrades (e.g.: changing from one major version like 15.0 to version 15.1) using a GUI and as easy as they can in Ubuntu.
gfxboot for grub2
a project by snwint
Make a final attempt to implement a graphical user interface for grub2 (gfxboot2).
ML and AI for code static analysis
a project by mvarlese
The idea is to explore the technologies and the various components to realize some AI to predict pitfalls in source code which can potentially generate run-time misbehaviours.
 md2jira: propagate workflow changes to an existing workflow instance
md2jira: propagate workflow changes to an existing workflow instance
an idea by lkocman
Currently not published outside of company (that would be also one of the goals).
House Daily Mutations Announcement System
a project by jaimegomes
The Goal is...
Investigate py-spy for OpenStack services profiling
an idea by tbechtold
py-spy is a python profiler (similar to pyflame (which is unmaintained)). The profiler can be used to create profiling data for running processes. This might be useful to find bottlenecks in OpenStack services.
Improve monitoring in internal infrastructure
a project by kbabioch
The monitoring in our internal infrastructure needs some love and attention. I want to spent some time during this hack week on the monitoring by fixing old checks, implementing new checks and making sure that those are configured and installed via configuration management.
Stream Radio Device
a project by zkalmar
Stream Radio device - It is built with Raspberry Pi Zero WH
Rados backend for NVMe
a project by hreinecke
Goal is to implement a rados backend in drivers/nvme/target. That will allow the NVMe target implementation to directly access Rados objects (ie export RADOS objects as namespaces), allowing third-party applications and/or OS to use NVMe-over-Fabrics to access a ceph cluster.
Out-of-the-box SPD support
an invention by jdelvare
In order to see the SPD (detailed memory information) data, the user currently has to manually load the needed kernel driver. Which driver to load depends on the memory type. Depending on the driver user, the devices may even have to be instantiated manually and this is a non-trivial multi-step task. Plus you need to be root to do it.
online DB of L3 supported products
a project by mvancura
The goal is to create a set of YAML files describing L3 supported products with all metadata we need to store there - and a JS presentation layer automatically showing this data in several forms, one of them will be a part of our L3 documentation.
Use C++ static analyzers for GCC codebase
an idea by marxin
I'm planning to experiment with clang-static-analyzer, cppcheck and maybe with coverity:
Type Check YaST with Sorbet
a project by mvidner
Sorbet is a gradual type checker for Ruby.
[Windows Subsystem for Linux] Build newest WSL-DistroLauncher in OBS
a project by lkocman
This is a task to update current WSL-Launcher (which can be already buildt in OBS) with latest-greatest upstream code https://github.com/Microsoft/WSL-DistroLauncher
Architecting a Machine Learning project with SUSE CaaSP
an invention by jordimassaguerpla
The goal of this project is to get an overview of the state-of-the-art technology on training and deploying machine learning projects with kubernetes and apply that to a SUSE CaaSP cluster.
Work on FPGA Acceleration for Cloud infrastructure
an idea by lyan
As we know, hardware accelerator is more and more important to AI/Machine Learning today, FPGA also comes to the front line beside with GPU. It is really helpful to understand its mechanism before deploying in a cloud environment.
Simplify implementations of lockless printk ring buffer
an invention by pmladek
There are attempts to solve some kernel deadlock with using lockless printk ringbuffer. The proposed implementation is pretty complex (6 stages, 6 write and 6 read barriers, two buffers, entries linked via list, ...)
Look at New Parallelisation Technologies
an invention by aschnell
The idea is to look at some technologies:
SUSana: debrand Grafana
an invention by pagarcia
Following trademark and licensing issues with Grafana, explore the possibility of debranding Grafana and use that in SUSE Manager (and maybe others)
Do Stuff with SUSE Raspberry Pi
an idea by cjschroder2
Install and test SUSE's Raspberry Pi distro on a Raspberry Pi 3 Model B. Explore the practical uses of stuffing a Linux distro on a bitty little single-board computer. Kiosk, digital signs, media server, gaming platform, digital photo frame, network attached storage...what is this little gadget good for?
Backup server on openSUSE in Raspberry Pi 3 with external USB mass storage
a project by bzoltan1
I would like to set up a small backup server on my spare hardware
Run VMs in CaaSP 4 cluster with SUSE-powered kubevirt
a project by jfehlig
This project aims to run VMs in a CaaSP 4 cluster using kubevirt and a libvirt+qemu container (aka compute container) based on SLES15 SP1/2. Compute containers based on openSUSE Leap15.1 and SLES15 SP1 already available in registry.opensuse.org and registry.suse.com respectively. VMs can be deployed to the cluster but there are several functional problems that need investigating, e.g. accessing the VM's serial and VNC consoles, proper network access, etc.
 Support Pinebook Pro in openSUSE
Support Pinebook Pro in openSUSE
an invention by michals
Updated almost 3 years ago. 3 hacker ♥️. 3 followers.revive qemu-devel.opensuse.org
an invention by mstrigl
qemu-devel.opensuse.org is a port forwarder to
Graphics support for SGI Octane
a project by tsbogend
With the approach of kernel 5.6 SGI Octanes are supported with builtin IO components. What's missing for a graphics workstation is a driver for the graphics card. There is already a not upstreamed framebuffer driver for Impact graphic cards. Since there will be no new framebuffer driver accepted upstream, the goal of this project is to convert the existing frame buffer driver to a DRM driver and make it ready to be sent upstream.
Install openSUSE Tumbleweed and set up hass on rpi4
a project by mlin7442
I got a Raspberry pi 4 not long ago, I'd like to install openSUSE Leap 15.2(Alpha) on it, and set up hass - Home Assistant, a open source home automation assistant on rpi4, then have some fun with it!
Bootable JeOS images for RISC-V
an idea by Andreas_Schwab
Create bootable JeOS images for RISC-V, for qemu and the HiFive Unleashed board. The existing images are set up for qemu linux-user emulation.
coreboot on Thinkpad Tx40p
an idea by persmule
Flash and optimize coreboot to t440p and port coreboot to t540p.
AI Piano
an idea by lin_ma
- Software involved: SLES 15 SP1 ARM + Tensorflow
 "Physical" notifications with Raspberry Pi and addressable LEDs
"Physical" notifications with Raspberry Pi and addressable LEDs
a project by dannysauer
I'd like a way to have a device on my desk which lights up to indicate that I have something I should be paying attention to. Initially, I'd like this to be for Office365 calendar events and GitHub mentions, but ideally it should support arbitrary messages. The plan is to assign specific colors (ideally "patterns" consisting of a sequence of colors and time) to specific message types.
 Migrate more OBS service scripts to pure systemd
Migrate more OBS service scripts to pure systemd
an invention by enavarro_suse
Following the work started in the last hackweek, Improve OBS service scripts, I will try to migrate current service script for workers to systemd unit, and at the same time, try to get rid of the sysv code.
Supportable Jetson Nano
a project by davidbyte
Whether it's building a newer, upstream UBoot, EDK II, or merely a SLE based rootfs, I want to make this platform a realistic possibility for desktop, digital signage, labs, etc.
openSUSE on ROCKPro64
a project by patrikjakobsson
The project aims to port openSUSE to the ROCKPro64.
Give avahi some love
a project by e_bischoff
Avahi is (among others) a domain names auto-configuration system for Linux compatible with Bonjour.
Btrfs OSD for Lustre
an idea by jeff_mahoney
Modern Lustre supports compelling features like snapshots but it requires OSDs to use ZFS in order to implement it. Since ZFS and Linux licensing is incompatible, it's not really a supportable solution.
UEFI/GRUB keyboard support on Raspberry Pi 4
a project by nsaenzjulienne
The USB controller (Via Labs 805 XHCI) on the RPi4 sits behind a PCIe bus which has no drivers at the moment in u-boot. After implementing it, we'll also have to make sure the USB HID is correctly connected with UEFI routines.
Investigate options to introduce Plugins to SUSE Manager
a project by cbosdonnat
For years we have been discussing the idea to modularize SUSE Manager. This would enable developers to create their own extensions to SUSE Manager without needing to touch the core repository.
Packaging libnvidia-containers and nvidia-container-runtime-hook
an invention by jordimassaguerpla
This is a follow up to https://hackweek.suse.com/projects/architecting-a-machine-learning-project-with-suse-caasp.
Nvidia GPU support for CaaSP
an idea by huizhizhao
Nvidia has a way to support GPU on Kubernetes via docker and crio, but so far they don't support SLES and CaaSP, this is the goal of this project.
uMEC Documentation - Architecture and Installation
a project by FSzekely
Overview
openSUSE Leap / TW / MicroOS / Kubic running on Freebox Delta
an invention by fcrozat
French ISP Free is providing a xDSL / Fiber modem, which includes a lot of features, including integrated NAS support and, more recently, allowing to run your own VMs (https://dev.freebox.fr/blog/?p=5450 sorry, in french)
SUSE @home Hands On Lab
a project by johnmpugh
Project Description
In the past year we've found ourselves in the middle of a pandemic, we merged two awesome companies together, and we have completely changed the trajectory of SUSE and Rancher. This project is intended to transfer knowledge of SUSE to Rancher and Rancher to SUSE for those who may be challenged with time and resources to try new things. This gives us a chance to explore other uses for Kubernetes all while taking advantage of older equipment (for use as workers) we may have to spare.
Linux on Cavium CN23XX cards
a project by tsbogend
Before Cavium switched to ARM64 CPUs they developed quite powerful MIPS based SOCs. The current upstream Linux kernel already supports some Octeon SOCs, but not the latest versions. Goal of this Hack Week project is to use the latest Cavium SDK to update the Linux kernel code to let it running on CN23XX network cards.
 Tumbleweed on Mars-CM (RISC-V board)
Tumbleweed on Mars-CM (RISC-V board)
a project by ph03nix
RISC-V is awesome, Tumbleweed is awesome, chocolate cake is awesome. I'm planning to combine all of them in one project.
Create openSUSE images for Arm and RISC-V boards
an invention by avicenzi
433 MHz to WiFi Gateway
an idea by rmax
Description
I want to replace the firmware on a 433 MHz to WiFi bridge ("Sonoff RF Bridge2") with an OpenSource firmware to allow it to communicate with arbitrary 433 MHz devices like remote switches and temperature/humidity sensors.
Looking for projects around:
armActivity